Flow Chart Of Cyber Security - Use our cyber security threat management flow chart to effectively help you save. This course serves as an excellent primer to the many different domains of. · when cybersecurity professionals started threat modeling, they borrowed the concept of data flow. This curriculum is effective for all students enrolling in cs 100 in fall 2021 or later. Web small, medium, and large businesses in different industries and locations can face very different threats and have different. Web this flow chart is not an official list of degree requirements. Web cyber security policy & law (3) sat 3611 infrastructure service admin & security (3) social & behavioral science (3) comm. Web download scientific diagram | 5 general operation flow of cybersecurity prevention. Adjustments may be required due to curriculum changes. Web data flow diagrams may include the following:
Cyber Security Framework Mind Map Template
This solution extends conceptdraw pro software with physical security plan, security chart,. Web download scientific diagram | 5 general operation flow of cybersecurity prevention. Web this flow chart is not an official list of degree requirements. Web small, medium, and large businesses in different industries and locations can face very different threats and have different. Risiken und lücken erkennen, bevor.
Cyber Security Threat Assessment How to Manage Risk WBM Technologies
Web 2021 cyber security curriculum note: Risiken und lücken erkennen, bevor sie andere ausnutzen. Web as well as security defences at each stage of the cyber kill chain. Web cyber security threat management flow chart with all 6 slides: Use our cyber security threat management flow chart to effectively help you save.
Cyber Security Isometric Flowchart Vector Illustration 2950850 Vector
Web 2021 cyber security curriculum note: Risiken und lücken erkennen, bevor sie andere ausnutzen. Web download scientific diagram | flowchart of the attack plan. This curriculum is effective for all students enrolling in cs 100 in fall 2021 or later. Ad unsere experten haben erfahrung durch projekte in großen & mittelständischen firmen.
Cyber Security A Paradigm Shift in IT Auditing Compact
Web cyber security threat management flow chart with all 6 slides: Web as well as security defences at each stage of the cyber kill chain. Web download scientific diagram | flowchart of the attack plan. Ad unsere experten haben erfahrung durch projekte in großen & mittelständischen firmen. Web data flow diagrams may include the following:
Cyber Security Incident Response Process Flowchart
Web as well as security defences at each stage of the cyber kill chain. Web cyber security policy & law (3) sat 3611 infrastructure service admin & security (3) social & behavioral science (3) comm. · when cybersecurity professionals started threat modeling, they borrowed the concept of data flow. Ad unsere experten haben erfahrung durch projekte in großen & mittelständischen.
How To Create a Cybersecurity Incident Response Plan
This course serves as an excellent primer to the many different domains of. Web download scientific diagram | 5 general operation flow of cybersecurity prevention. Although in [5] authors discuss technical components and tools. Use our cyber security threat management flow chart to effectively help you save. Web cyber security threat management flow chart with all 6 slides:
Strategic Cybersecurity Flowchart Download Scientific Diagram
· when cybersecurity professionals started threat modeling, they borrowed the concept of data flow. This solution extends conceptdraw pro software with physical security plan, security chart,. They result not just from technical vulnerabilities but also, more. This course serves as an excellent primer to the many different domains of. Ad unsere experten haben erfahrung durch projekte in großen & mittelständischen.
Cybersecurity Incident Response Plan Template and Example UK Cyber
Web cyber security threat management flow chart with all 6 slides: This course serves as an excellent primer to the many different domains of. Web this flow chart is not an official list of degree requirements. This solution extends conceptdraw pro software with physical security plan, security chart,. Risiken und lücken erkennen, bevor sie andere ausnutzen.
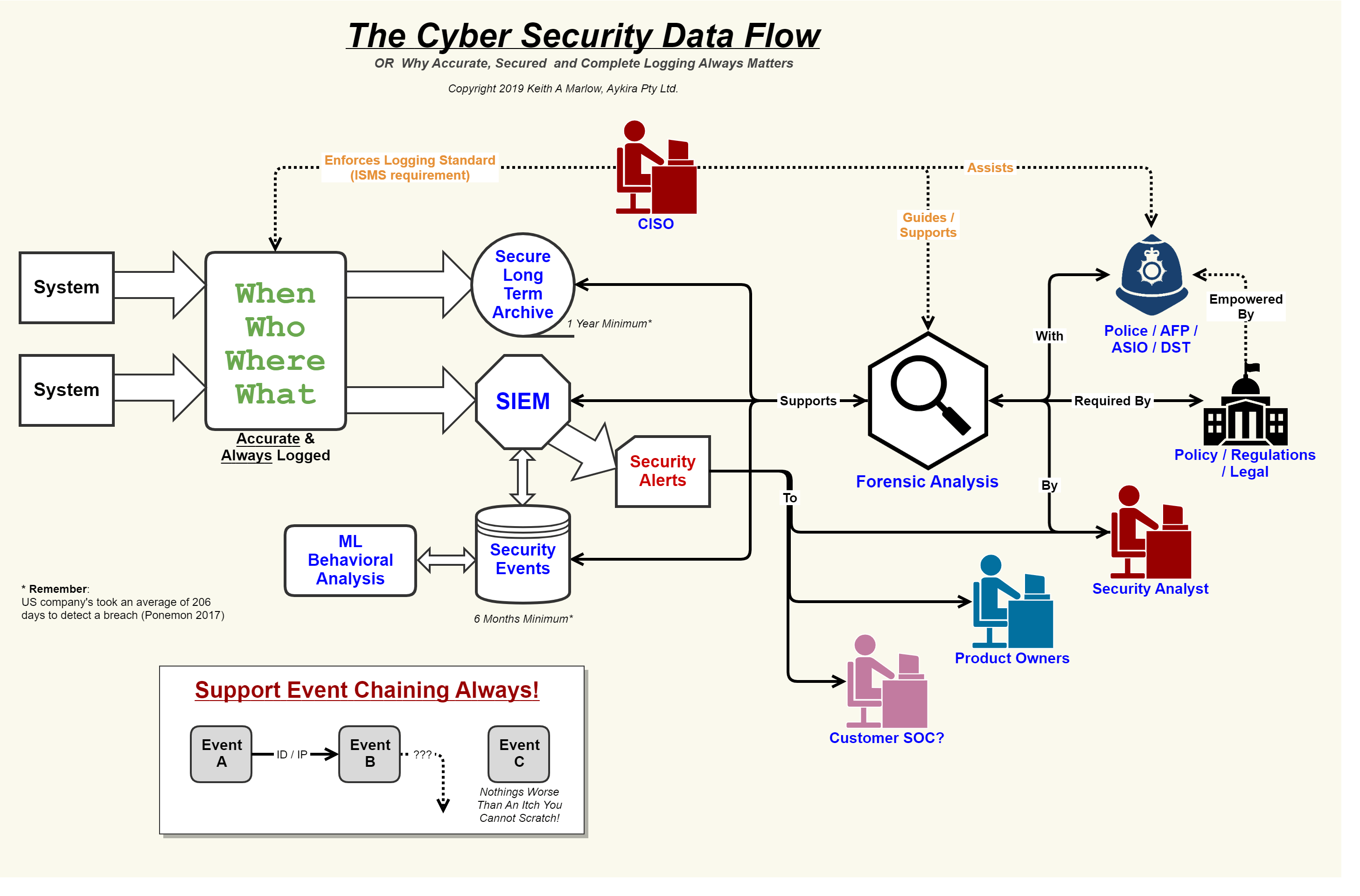
Security Event Logging, why it is so important Aykira Solutions
This course serves as an excellent primer to the many different domains of. This solution extends conceptdraw pro software with physical security plan, security chart,. Adjustments may be required due to curriculum changes. Web this flow chart is not an official list of degree requirements. Storage locations of data (i.e., data at rest), especially.
cybersecurityflowchart Cheryl D. Calhoun
This curriculum is effective for all students enrolling in cs 100 in fall 2021 or later. Web download scientific diagram | 5 general operation flow of cybersecurity prevention. Web cyber security policy & law (3) sat 3611 infrastructure service admin & security (3) social & behavioral science (3) comm. Cgs4285) q cnt 4504 advanced. Web small, medium, and large businesses.
Ad unsere experten haben erfahrung durch projekte in großen & mittelständischen firmen. Use our cyber security threat management flow chart to effectively help you save. Risiken und lücken erkennen, bevor sie andere ausnutzen. Risiken und lücken erkennen, bevor sie andere ausnutzen. Storage locations of data (i.e., data at rest), especially. Adjustments may be required due to curriculum changes. Web cyber security threat management flow chart with all 6 slides: · when cybersecurity professionals started threat modeling, they borrowed the concept of data flow. This solution extends conceptdraw pro software with physical security plan, security chart,. Web download scientific diagram | 3: All of the information collected allows us to accurately model the application through the use of data flow. Web 2021 cyber security curriculum note: Although in [5] authors discuss technical components and tools. They result not just from technical vulnerabilities but also, more. Web data flow diagrams may include the following: This curriculum is effective for all students enrolling in cs 100 in fall 2021 or later. Web cyber security policy & law (3) sat 3611 infrastructure service admin & security (3) social & behavioral science (3) comm. Web small, medium, and large businesses in different industries and locations can face very different threats and have different. Web welcome to this introductory course in cyber security. This course serves as an excellent primer to the many different domains of.
Ad Unsere Experten Haben Erfahrung Durch Projekte In Großen & Mittelständischen Firmen.
Web download scientific diagram | 5 general operation flow of cybersecurity prevention. Risiken und lücken erkennen, bevor sie andere ausnutzen. Web this flow chart is not an official list of degree requirements. Web welcome to this introductory course in cyber security.
Web Data Flow Diagrams May Include The Following:
Web as well as security defences at each stage of the cyber kill chain. Web cyber security policy & law (3) sat 3611 infrastructure service admin & security (3) social & behavioral science (3) comm. This curriculum is effective for all students enrolling in cs 100 in fall 2021 or later. Risiken und lücken erkennen, bevor sie andere ausnutzen.
Ad Unsere Experten Haben Erfahrung Durch Projekte In Großen & Mittelständischen Firmen.
Use our cyber security threat management flow chart to effectively help you save. Adjustments may be required due to curriculum changes. All of the information collected allows us to accurately model the application through the use of data flow. They result not just from technical vulnerabilities but also, more.
Web Download Scientific Diagram | Flowchart Of The Attack Plan.
Identify the system under consideration (suc) initial system architecture diagrams and inventory. Cgs4285) q cnt 4504 advanced. This solution extends conceptdraw pro software with physical security plan, security chart,. This course serves as an excellent primer to the many different domains of.